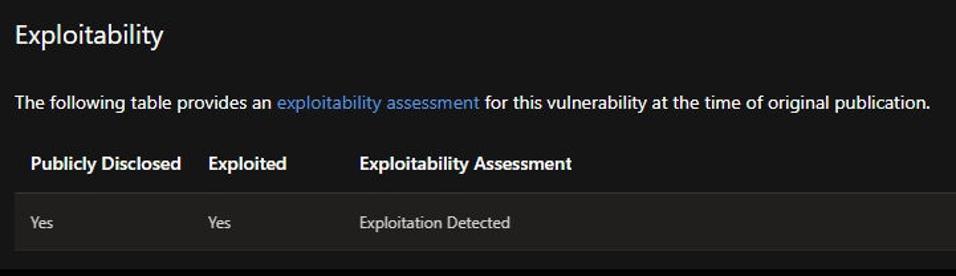
Microsoft has warned Windows 10 users that a previously unknown, and therefore unpatched, security vulnerability is being exploited by cybercriminals. The zero-day is a high-rated vulnerability (falling just short of critical) that could allow an attacker to remotely execute code on the target computer and potentially gain complete control.
Additionally, Microsoft has confirmed that cybercriminals are known to be already exploiting CVE-2021-40444 and advises users to take speedy mitigation action until an official patch becomes available. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is following Microsoft's lead and also "encourages users and administrators" to "implement the mitigations and workarounds."
The latest Windows zero-day vulnerability explained
The vulnerability itself sits within the Internet Explorer browser rendering engine, MSHTML, which might sound like a good thing. After all, nobody uses Internet Explorer anymore, right? Wrong. Microsoft Office documents also use that rendering engine, and that's where the attackers are aiming the exploit. The zero-day was reported to Microsoft on the morning of Sunday, 5 September, by a researcher at EXPMON. The exploitation detection company tweeted that Office users should be "extremely cautious" about files until a patch is made available.
The attackers are using Office documents that load MSHTML when opened to render a specially constructed malicious web page and employ an ActiveX control to download the malware payload. Users without administrator rights will be less impacted than those with greater privileges, of course.
"Although this attack does require user interaction," Scott Caveza, a research engineering manager at Tenable, says, "threat actors are likely to target victim organizations with tailored emails or attempt to exploit current news events for a higher success rate."
You can read a technical deep dive into multiple documents infected by this exploit here.
Attackers look for products that fit big shoes
As I note in the Straight Talking Cyber video at the start of this article, Microsoft tops the charts for published security vulnerabilities, with Windows 10 being the Microsoft product with most of them. This in and of itself is not necessarily surprising. "One of the reasons for this spike in zero days is that Microsoft is among the most ubiquitous business software in the world," Sam Curry, the chief security officer at Cybereason, said. "If you're an attacker and want victims, you go after the biggest footprint." Windows 10 and Microsoft Office certainly fit into those shoes.
No patch yet so apply this workaround instead, Microsoft says
As this latest attack shows, opening Office documents from untrusted sources is always a risky and not recommended business. The good news is that both Microsoft Defender Antivirus and Microsoft Defender for Endpoint provide detection and protection, Microsoft has stated. Hopefully, a patch will be made available as part of the Patch Tuesday cycle next week, or even as an out-of-band update beforehand although that looks increasingly unlikely.
Approached for further guidance, a Microsoft spokesperson said, "we have identified a limited number of targeted attacks," and pointed me towards the security update guidance page which contains a workaround. This involves disabling Internet Explorer ActiveX controls by updating the system registry.
However, former senior threat intelligence analyst at Microsoft and well-known security researcher, Kevin Beaumont, has tweeted that he managed to modify a one-click attack sample so that it could bypass the Microsoft workarounds.
Threat intelligence specialists, Cyjax, confirms that several security researchers have already successfully created exploits and warn that further attacks could be imminent.
Patch Tuesday can't come quickly enough, it would seem.