- KONNI hackers use KakaoTalk to deliver malware and harvest account credentials from victims
- Attackers exploit Google Find Hub to remotely wipe Android devices and evade detection
- Compromised PCs spread malware to contacts while mobile devices are repeatedly factory reset
North Korean threat actors with ties to the government were seen resetting target Android devices to factory settings to cover their tracks.
Researchers from Genians said they saw these attacks in the wild, targeting primarily individuals in South Korea, carried out by a group called KONNI (named after a remote access tool it is using)
The researchers say KONNI has “overlapping targets and infrastructure” with both Kimsuky, and APT37, known North Korean state-sponsored actors.
Wiping the device
The attack starts on KakaoTalk messenger, one of the most popular instant chat messaging platforms in the country, where KONNI’s agents impersonate trusted entities like the National Tax Service, or the police.
During the conversation, they send a digitally signed MSI file (or a ZIP archive with it) which, if the victim runs it, launches a script that ultimately downloads different malware modules, including RemcosRAT, QuasarRAT, and RftRAT.
These RATs harvest all sorts of information from the compromised device, including Google and Naver account credentials which are then used to log into the victim’s Google account.
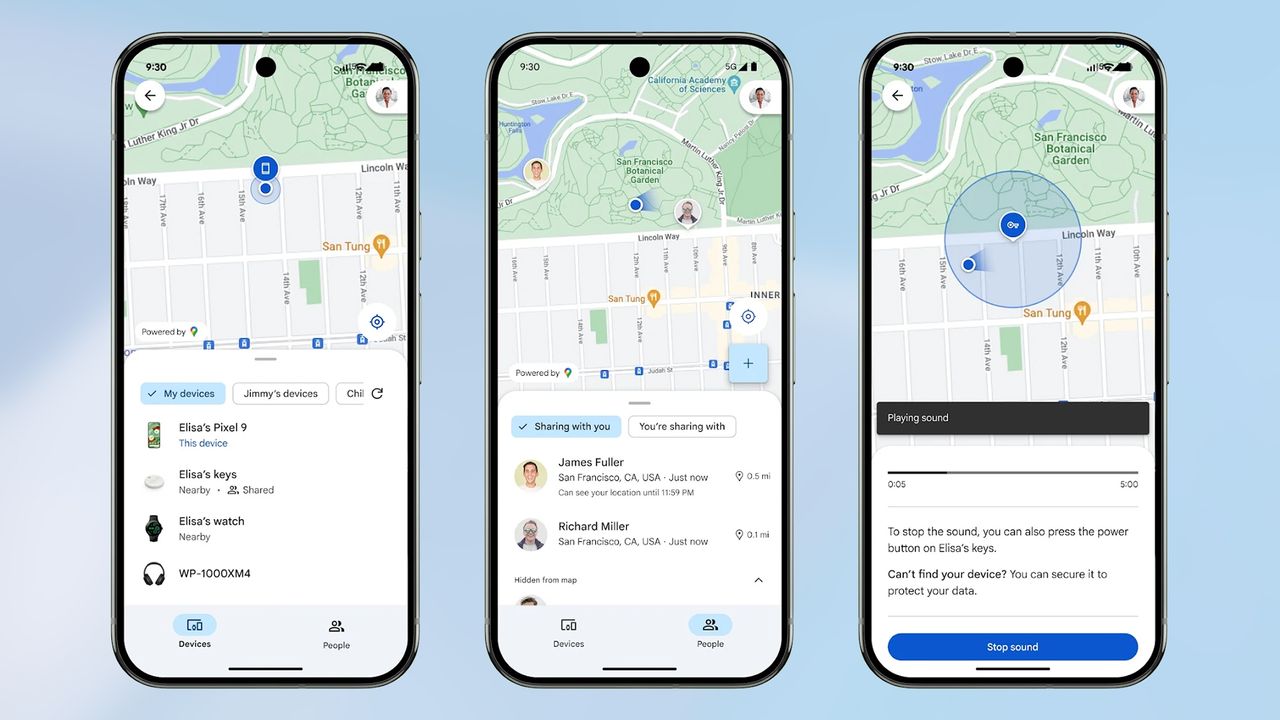
From there, they access Google Find Hub, a built-in tool that lets users remotely locate, lock, or wipe their devices, and use it not only to view all other registered Android devices, but also to track the victim’s location.
When they see the victim out and about, and unable to quickly address an attack, they send remote factor reset commands to all devices, erasing data, disabling alerts, and disconnecting the victim from the KakaoTalk PC sessions. The wipe is done three times.
With the mobile device wiped but the KakaoTalk PC session still active, the hackers use the compromised computer to send malicious files to the victim’s contacts, spreading the infections further.
The motive behind the attack is unknown at the time, but state-sponsored threat actors are usually engaged in cyber-espionage and disruption.
Via BleepingComputer
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.








