
That's all for our live coverage of Infosec 2025.
If you missed Infosec this year, or didn't have time to see everything you wanted, don't worry - we have you covered!
We went live for all three days of Infosec this year, and saw everything that the conference had to offer. Infosec is one of the biggest security events on the calendar, and this year didn't disappoint - catch up with our thoughts below!
Good morning from InfoSecurity Europe 2025! We're here at the Excel, and off to collect our badge before heading in.
Despite it being June, it's a cloudy and blustery day here - let's hope things are warmer inside...

We're heading in to the show now!
As you can see from our pictures, the theme of Infosec 2025 is "Building a Safer Cyber World" - something you can bet we'll hear more about over the next few days.


We're now seated for a super packed keynote, plenty of people are standing - so this is clearly a popular one! We're about to hear from Graham Cluley, host of the Smashing Security Podcast who'll introduce us all to Infosec's 30th year!
There's a quick look back to how far cybersecurity has come in the last 30 years before Cluley explains that hackers aren't girlfriend-less men in garages anymore (his words!), but are serious, state sponsored actors - outlining an almost unrecognisable evolution in that InfoSec has helped to guide security experts through.

Now, we're listening to Professor Brian Cox who's talking us through the link between cosmology and cybersecurity and computing. General relativity, the theory of space and time, and cosmology all link closely to quantum computing - with complex mathematics, data sets, and quantum mechanics.
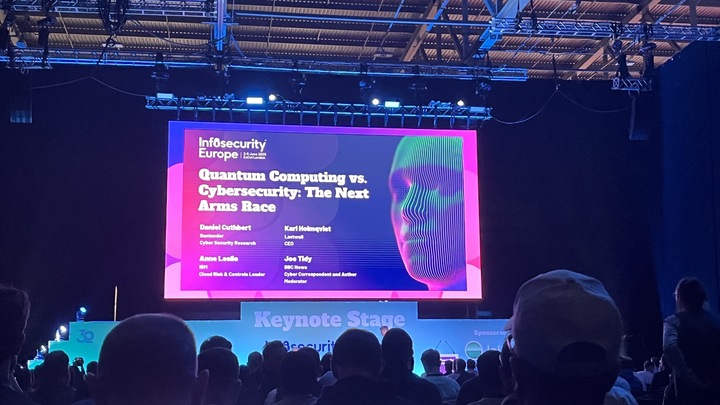
Next, it's 'Quantum computing v Cybersecurity' - chaired by BBC News' Joe Tidy. Here, cybersecurity is described as an 'Arms Race' - although not everyone think that terminology is helpful!
There's a myth, panel expert and Lastwall CEO Karl Holmqvist explains, that quantum computers can break any encryption. But really, at the moment, quantum computers can decrypt several commonly used encryptions - encryption will look different in the age of quantum, but it could still be effective. Cryptography will remain an important facet of cybersecurity for a long, long time - he argues.
"Harvest now, decrypt later" is a huge talking point. The industries most at risk (unsurprisingly) are the 'critical national' warns Daniel Cuthbert - panel participant and cybersecurity expert. That means healthcare, finance, and telecoms could face serious difficulties in a PQC (post-quantum cryptography) world.

Next up - we're listening to Paul Chichester and his take on the 'Cyber Cold War' and the geopolitics of cyber threats. Paul is the Director of Operations at the NCSC - so investigating cyber threats is his bread and butter.
As everyone knows, geopolitics is key to the cyber landscape. Cyber operations are now one of the go-to tools for covert state campaigns. Conflicts today are powered by cyber capabilities. Chichester points to the Viasat offensive in the Russian war in Ukraine as a prime example, and he explains that targeted attacks are increasingly disruptive, especially in the case of Russia, which are focusing on the logistical supply chain of materials into Ukraine.
Good cybersecurity has helped Ukraine, namely in the recent drone attack, which seemingly took Russia entirely by surprise. This shows the importance of great cybersecurity, Chichester argues. Defence, when done right, can be a vital weapon.
Beyond state sponsored attacks and espionage, states are using cyber capabilities for sabotage and coercion. Real world sabotage used cyber as a tool to inform operations. Volt Typhoon, Chichester points out, is a perfect example of how geopolitics threatens critical infrastructure. States are understanding that penetrating critical infrastructure will likely form the basis of conflict in the future.
So what's the takeaway? Well, it's that geopolitics should inform your cyber strategies as security team - so make sure to integrate this conversation into your risk management and global footprint landscapes.
Now, a little break from the keynote stage and on to exhibition floor for some showcases and introductions!

First, we're headed to Okta, who are talking us through their AI-driven identity threat protection. Okta are keen to tell us about the shared risk signals, which allow a security event provider to transmit risk signals to Okta, enabling customers to use these to uncover potential identity threats in their ecosystem. "Years ago, attackers used to hack systems, now they log in", Okta warns.
Rubrik is next up, showcasing its data resilience and data security solutions for cyber recovery. Rubrik talks me through the devastating effects of ransomware on companies, particularly recently for retail organisations, and the importance of cyber recovery. A robust cyber recovery plan can mean a firm goes from a thirty day recovery, to just a 48 hour bounce back, Rubrik explains.
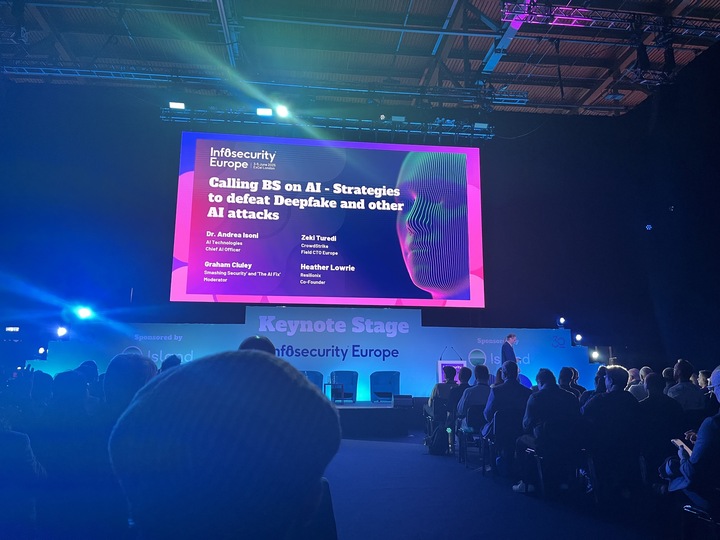
Here we're listening to ‘calling BS on AI’, a panel about how agentic and generative AI are affecting the threat landscape.
Most people think that AI is powering organisations in a novel way, but that’s not quite true - says Zeki Turedi, CrowdStrike's Europe Field CTO. AI is just facilitating threat actors in their attacks, but it’s not revolutionising the way attacks are leveraged. Attackers are more efficient and quick thanks to AI - but it uses existing capabilities.
One of the biggest factors for AI is the damage in trust. Deepfakes, for example, are eroding trust all round and are a disruptive force - but generative AI’s.
Dr Andrea Isoni introduces a pretty shocking statistic - 30-40% of web traffic is malicious bot traffic, meaning the treat of data theft is ever present for organisations with these trawlers looking to exfiltrate as much as possible.
The main question is how fast this will change. Generative AI is in its infancy, and the trend of more sophisticated deepfakes, like the impersonation attack we saw on Susie Wiles, are only likely to get more potent in future. Organisational processes and training will be a huge factor for CISOs going forward.

Next up, we're visiting Cloudflare, which claims to bring "everywhere security" to its customers. Specifically, this refers to the company's unified cybersecurity platform that protects users from "Network to Cloud, Apps to AI". Cloudlflare recently introduced a set of E2E PQC protections which helps organisations with safeguarding network traffic - PQC continues to be at the forefront of conversations so far at Infosec 2025!

Finally for today, we’ve taken a quick stop at DarkTrace, where they’re giving a mini-talk and overview about the difference between reactive and proactive network security. Staying ahead of attacks and understanding your cloud security posture is crucial, DarkTrace argues - and the right role permissions and access controls are key to protecting from insider threats.
Good morning and welcome to day 2 of our Infosec 2025 coverage!
We're back at the Excel and ready for another packed day, so stay tuned for all the latest updates throughout the day...

Having a quick look around this morning before the first keynote. The Cyber Strategies stage is setting up, blasting Lana Del Rey's 'Say Yes to Heaven' (which, to be fair, is her best song). Everyone is clearly gearing up for another packed day!

Keynote number one today, and it's Rory Stewart with his look at cybersecurity through the geopolitical lens.
We're hearing about the Morris Worm and Love letter cyberattacks (before my time, I'll admit) and the origins of the Five Eyes Alliance, reminiscing about the humble beginnings of cybersecurity and the internet itself, and just how far security has come.
The consequences of smartphones on international relations, Stewart says, are huge. He points to revolutions in Syria and Tunisia (the Arab Spring) and the erosion of borders. This is followed by a polarisation of voters and erosion of trust in media - he draws a direct line from the invention of the smartphone to the collapse of governments and the rise of far right parties today.
Stewart points to the StuxNet attack as a turning point for cybersecurity - state-on-state cyberattacks became more dramatic in this period and cyber began to be truly weaponised.
Moving on to 2014, we see the impact of this period not just for cybersecurity but for geopoloitics - with populists elected all around the world in in the 2014-2020 period. Cyber begins to become a tool for election interference in this period too - Stewart describes this as a "collapse of global norms."

For cybersecurity this means more risk. Decreased funding for universities, for government agencies, and a reduction in regulations means danger and unpredictability for cybersecurity. Defunded research also means a lack of tools to counter this.
Stewart finishes with a prediction. He outlines the collapse of the "rules-based international order" and predicts significantly more frequent and potent state-on-state cyberattacks and conflicts. Social media and AI will accelerate these, he warns, and election interreference on an unprecedented scale thanks to deepfakes.

Back to the floor! And the first stop is ThreatLocker, an enterprise cybersecurity solutions firm, is showcasing its visibility control and endpoint protection platforms. The new features that it wants to show off are in patch management and web control solutions. Recently launched, the Web Control is boasted as a "seamless web control solution built directly into the ThreatLocker platform."
We're here with 1Password now, who are talking me through the updates to their Extended Access Management - which was launched over a year ago but is evolving with the acquisition of Trelica, a SaaS access management company. The move from a password manager to access & identity management is in line with a shift in cyberattacker tactics, 1Password explains - keeping up with threat actors means evolving security products and frameworks.
We're here at NordVPN, where they're explaining the importance of dark web monitoring. Dark web chatter, like mentions of a C-Suite executive, company name, or ransomware gang, can be an indication that an attack is imminent - but its often neglected in protection software. Nord's NordStellar plan integrates this for businesses, as well as digital attack surface monitoring and compromised credential detection.

We're visiting Check Point next, where they explain their new Firewall tools. The AI-Powered Firewall scans through your company's protocols and network to identify points of weakness anomalies. The AI systems learn on the job, and adapt to deliver better detection capabilities and incident response.

Next, we're hearing from DataMinr. They're explaining their news room alert tool, which scrapes millions of data sources to send to news organisations in order to bring them super-quick incident alerts. Over 1,500 newsrooms around the world use this technology, including the BBC, Al Jazeera, and the New York Times. They verify the data by cross referencing news sources and monitoring online chatter - although this seems a pretty tall task given the speed at which misinformation can spread online.
LastPass is here and is showcasing its new SaaS Monitoring tools for ground level control with high-level app visibility. This, LastPass explains, helps businesses eliminate security blind spots and gives them complete control over their entire SaaS footprint - streamlining their visibility and saving them money by optimizing technology costs. This was launched just a few weeks ago and is available for businesses now.

Now, this might look like the world’s most sensible silent disco, but we’re actually listening to a talk by Hannah Baumgaertner, Head of Research at Silobreaker talk about the geopolitical influence on the cyber landscape - a popular theme at Infosec this year!
Baumgaertner explains that the lines between Hacktivism and state-sponsored operations have been blurred given the targeting of critical infrastructure and government institutions. DDoS, botnets, and data leaks are common features of modern conflicts. Not just within conflicts though, as hacktivists are targeting elections to disrupt and influence election results.
It’s a stop with ISACA next, where they’re keen to tell me about the certifications in AI Audit, Security Management, and Certified Cybersecurity Operations Analysis. We're told this is two years in the making and recently released - based on industry feedback and research. ISACA goes beyond just certifications, training and study materials, and really offers a community of leaders and experts. Particularly interesting is the SheLeadsTech initiative that pushes for gender diversity and female leadership within the IS/IT communities - take a look at their stall if you get a chance - you won’t find a friendlier group!
Mike here - I'm over at the Micrososft stand, listening to a talk by CyberOne CEO Dominic List and England rugby legend Dylan Hartley.
You might be wondering - what's the correlation between cybersecurity and rugby?
"I couldn't find any", Hartley laughs - luckily, we're interviewing him shortly so will drill for more!

Ellen taking back over, and I'm doing something a little bit different this afternoon - I'm with Semperis for what they call "Operation 999". This is a ransomware simulation, focused on the water industry. Given recent attacks on critical infrastructure and the rise in geopolitical tensions - cyberdefense for public will be quite literally a matter of life and death for many people.

The first rule is enjoy yourself and have fun, Semperis says, although Yossi Rachman, Director of Security Research. He’s leading the exercise, calls himself the ‘dungeon master’, and they’re about to simulate a randomsware attack designed to make participants ‘sweat a little bit’, so you make your own mind up about this.
There's a red and a blue team, who are given briefings in rounds that they then must respond to. The aim is for the blue team to defend and adapt to the challenges the red team throws given the context provided by Semperis. We've just learnt that the blue team has identified anomalous behaviours and their plan to prepare for a possible attack - next we'll hear what the red team has in store for them.

The red team is all-systems go, credential stuffing to gain access then dropping malware tools, disrupting comms, exfiltrating data using Cobalt Strike C2 and causing as much chaos as they can - all while attempting to evade detection.
There's a fair bit of creativity involved with this exercise- with the red team able to throw in new attacks or features. Participants say that this kind of training is key to testing security team's readiness. Semperis is throwing unpredictable new facets to the scenario to keep both sides on their toes - which is what makes the simulation so useful. Real ransomware attacks are seriously unpredictable, so your training should be too.
As we wrap up, you'll be happy to hear that the blue team has refused to pay the ransom. But, the red team have played this smart. Posing as ethical hackers, exposing dodgy bonuses and discriminatory behaiviour, even going as far as to short the water company's stock - there's definitely a lot of ideas, strategies, and tactics being swapped and learnt. Despite the casual atmosphere, there's plenty of seriously informative conversations on both sides - and the debriefs have brought the participants together to discuss everything they've taken from the exercise.
In the end, I think the red team have this one - but given the the lessons learnt for both teams (and me!) next time could be very different.
We're here at InfoSec for its third and final day, and although it's definitely a bit quieter here today, we're looking forward to hearing the keynotes and getting to see some of the busier stands!

We're hitting up HackerOne first - where they explain their pentesting and white hat ethical hacking events. Testing vulnerabilities is more important than ever, and HackerOne connects organisations with over 2 million security researchers to help them get the most out of their bug bounty programmes.
We're taking a look at Bridewell, which works primarily with critical infrastructure bringing cybersecurity consultancy, data privacy services, and penetration testing to make sure national infrastructure is secure and prepared. Everyone will be familiar with the significant challenges threatening critical infrastructure especially given the global political climate - so Bridewell's mission to keep infrastructure safe could quite literally save lives by protecting energy, water, and nuclear facilities.

For Privileged Access Management, Keeper Security is offering a whole host of features like credential and file management, critical system protection, continual threat monitoring, and streamlined third party access. With clients in a range of industries like insurance, education, and finance, on show today is the company's partnership with F1 giant Williams. Plenty of stands this year are partnered with F1 teams this year at InfoSec, but as a Williams fan myself, Keeper Security is by far my favourite!
Next, we're at OneTrust to hear about their spring release which uses AI to help organisations with data governance and compliance as well as risk management. They emphasise security with this new release in the face of a threat landscape that seems to be growing ever-more dangerous. New and existing regulations can be a challenge for even the most organised firms - but OneTrust aims to make reliable data governance a bit more simple.
Next, we're swinging by Hadrian - a Dutch based start-up, delivering an AI-powered offensive security platform for external attack surfaces. Founded by ethical hackers, Head of Demand Generation Ayanda Chiwuta explains, Hadrian offers an agentless AI platform that deploys in minutes. The use of AI models, he says, help them predict the next attack vector more readily.

For the final speech of the day, we’re heading over to the silent disco stage (Cyber Strategies) for Keeper Security’s Darren Guccione who’ll be speaking about the Future of Defence report and a range of issues in cybersecurity.
92% of IT and Security leaders have seen an increase in attacks and threats, and unsurprisingly, 52% of professionals have seen AI powered attacks and 36% have seen supply chain attacks - statistics that won’t come as a surprise to other IT leaders.
Guccione says 35% of security teams lack the defences to defend against these types of attacks, so teams aren’t nearly as prepared as they should be. Two firms per minute are paying a ransom from a ransomware attack, he explains, so these security failings are having a serious real-world affect.
Traditional layered cybersecurity solutions don’t stop data breaches, he explains. Inadequate visibility, security, control, compliance, and reporting all play parts in vulnerabilities. A zero-Trust strategy approach is needed to mitigate these risks, with zero standing privilege helping prevent attackers from permitting organisations horizontally. Zero knowledge means the security vendor should never have access to decryption keys, so everything is stored and managed client side to ensure security.
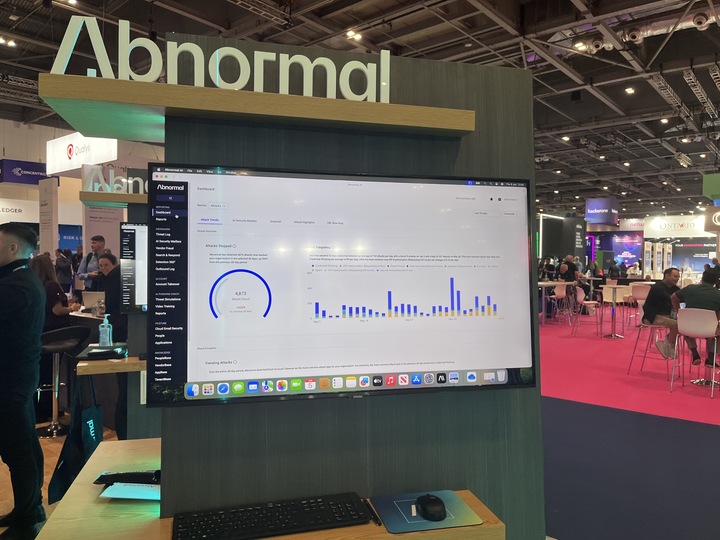
A few final stops and we're at Abnormal AI (formerly Abnormal Security), a cloud email security platform founded in 2019 with over 3,000 customers. Abnormal brings a behavioural approach to email security, and leverages the AI to protect customers against social engineering attacks and account takeovers.
We’re also taking a look at HornetSecurity - who are a Microsoft 365 based data backup and security platform. A Salesperson tells me that at their InfoSec stand this year there’s been a huge interest in their people protection product, which provides staff training to help with social engineering awareness, as well as Permission Manager for access management and visibility.
For a little hardware, we're talking to Apricorn's John Feilding - who very kindly talked me through all of their encrypted USB and storage solutions. These devices have a physical pin pad and are completely software-free, so are the perfect choice for backup storage in the event of a ransomware attack, for example. They operate across a whole number of industries, but are particularly effective in sectors that use sensitive data and need highly secure, on-device security. If you're looking to an alternative to the ever more expensive cloud storage, check out Apricorn!
That’s a wrap for us for InfoSec 2025 - thanks to the organisers for putting it all together and thanks to everyone who chatted to TechRadar Pro over the last three days, and of course, thanks to all of you who read along! We hope to see some of you at the next one!








