
The idea of someone digging through trash sounds almost ridiculous—until it suddenly doesn’t. One tossed receipt, one old device, or one casually discarded envelope can flip from harmless clutter into a full-blown security risk in seconds. That bin sitting quietly in the corner or out by the curb holds more than waste; it holds fragments of daily life that tell a story. And the wrong person can piece that story together faster than most people expect.
Information theft rarely kicks down the front door anymore. It creeps in through overlooked cracks, and trash sits right at the top of that list. People lock phones, update passwords, and install security apps, yet forget the simplest vulnerability waiting to be picked apart.
1. The Paper Trail That Refuses to Stay Quiet
Paper might feel old-school, but it still carries a shocking amount of sensitive information. Bank statements, credit card offers, medical bills, and even shipping labels reveal names, addresses, account numbers, and spending habits in plain sight. Tossing these documents straight into the trash hands over a ready-made identity kit to anyone willing to sift through it. Many people assume that ripping paper once or twice solves the problem, but determined thieves can easily piece together torn documents like a puzzle.
Receipts create another surprising vulnerability. Retail receipts often display partial card numbers, store locations, and timestamps that help build a profile of shopping behavior. Combine that with a name or address found elsewhere in the trash, and suddenly the puzzle starts forming a clear picture. Even loyalty program details printed on receipts can connect dots that lead back to online accounts. That connection gives thieves more than enough to attempt password resets or phishing attacks.
The fix doesn’t require a complete lifestyle overhaul, but it does demand consistency. A cross-cut shredder turns sensitive documents into confetti that nobody wants to reconstruct. Digital statements reduce the paper flow significantly, which cuts down on risk before it even starts. Taking a few extra seconds to remove labels from packages or black out personal details adds another layer of protection. Trash should never tell a story about someone’s life, and these simple habits keep it that way.
2. Old Tech, New Problems
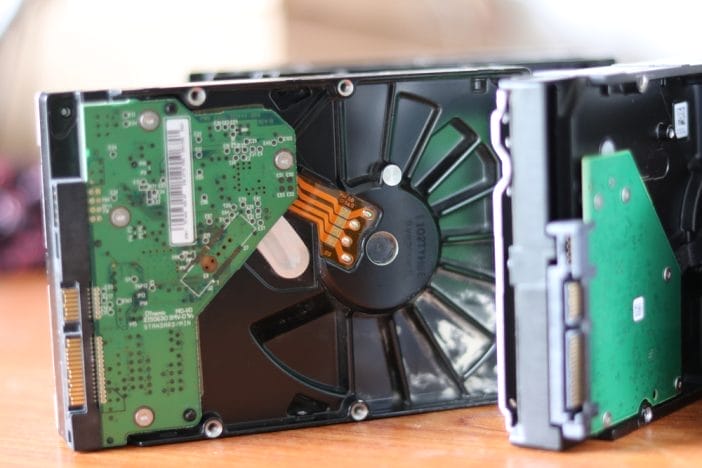
That dusty phone sitting in a drawer or the laptop headed for the trash still holds more secrets than expected. Devices store emails, saved passwords, browsing history, photos, and sometimes even financial documents. Deleting files or performing a quick reset does not always erase data completely, which leaves room for recovery with the right tools. Tech-savvy thieves know exactly how to extract that leftover information, and they often target discarded electronics for that reason.
Hard drives and storage cards present an even bigger risk. People often forget about external drives, USB sticks, or memory cards tucked into drawers, only to toss them out during a cleanup spree. These tiny devices can hold years of data, including backups of entire systems. Even something as simple as a printed QR code saved on a device can link directly to accounts or payment platforms. Once that data lands in the wrong hands, it becomes incredibly difficult to control where it goes.
Safe disposal of electronics requires more than a trip to the curb. A full factory reset combined with secure data-wiping software dramatically reduces the chances of recovery. Physically destroying storage devices adds another layer of security, especially for older hardware. Many electronics retailers and recycling programs offer secure disposal services, which makes the process easier and safer. Treating old tech like a vault of personal information ensures that nothing valuable slips through the cracks.
3. Junk Mail That Isn’t So Junky
Junk mail often feels like nothing more than an annoyance, but it can serve as a goldmine for identity thieves. Pre-approved credit offers, insurance letters, and promotional mail frequently include personal details that confirm identity markers. Names, addresses, and even partial financial information appear in these documents, which helps criminals verify stolen data or build convincing scams. Tossing these items unopened might feel satisfying, but it also leaves them completely intact.
Credit card offers deserve special attention because they sometimes require minimal effort to activate. A thief who finds one in the trash might attempt to intercept or redirect it, especially if other personal details appear nearby. That situation can spiral into unauthorized accounts opened in someone else’s name, creating a headache that takes months to resolve. Even something as simple as a catalog subscription can confirm a valid address and name combination.
Stopping this risk starts with reducing the flow of junk mail in the first place. Opting out of pre-screened credit offers and marketing lists significantly cuts down on incoming mail. Shredding or securely disposing of anything that includes personal details adds a second layer of defense. Taking a moment to review what arrives in the mailbox turns a passive habit into an active security step. Junk mail might look harmless, but it carries more weight than expected.
4. Packaging That Spills Too Much
Online shopping has turned cardboard boxes and padded envelopes into everyday items, but those packages often reveal more than intended. Shipping labels display full names, addresses, and sometimes phone numbers, which gives thieves a direct line to personal information. Even the type of product ordered can hint at lifestyle habits, financial status, or interests. Leaving those boxes intact in the trash creates an easy opportunity for someone to collect valuable details without much effort.
High-value items make the situation even riskier. Packaging from electronics, luxury goods, or specialty equipment signals that something valuable might be inside the home. That information can attract not only identity thieves but also burglars looking for their next target. A stack of branded boxes sitting by the curb can act like a billboard advertising what’s inside. That visibility turns a simple disposal habit into a potential security issue.
Breaking down boxes and removing labels reduces that exposure immediately. Cutting labels into pieces or using a marker to obscure details prevents easy identification. Recycling centers often accept flattened boxes, which adds an environmentally friendly bonus to the process. Keeping packaging discreet ensures that trash doesn’t double as a public announcement of personal purchases. A little effort here keeps curiosity from turning into something more serious.
5. Medical Information That Should Never Wander
Medical documents carry some of the most sensitive information a person can have, yet they often end up in the trash without much thought. Prescription labels, appointment summaries, and insurance statements include names, dates of birth, and health details. That combination creates a powerful tool for identity theft, especially when used for medical fraud. Criminals can use this information to obtain prescriptions, file false claims, or even create fake identities tied to real medical histories.
Prescription bottles pose a unique challenge because they often display personal details directly on the label. Tossing them without removing or covering that information leaves it fully visible. Even empty packaging from over-the-counter medications can hint at health conditions or routines. That insight might seem minor, but it can contribute to targeted scams or phishing attempts that feel alarmingly personal.
Protecting medical information starts with treating it like financial data. Removing labels from prescription bottles or scratching them off ensures that nothing readable remains. Shredding medical documents prevents reconstruction and keeps details private. Many pharmacies offer safe disposal programs for medications and packaging, which adds another layer of security. Health information should never wander beyond its intended use, and careful disposal keeps it contained.
6. The Subscription Trap Sitting in Plain Sight
Subscription services have quietly woven themselves into daily life, from streaming platforms to meal kits and fitness programs. The packaging and paperwork tied to these services often include account numbers, usernames, or billing details. Tossing these materials without a second thought can expose ongoing services that link directly to payment methods. That connection creates an easy entry point for anyone looking to exploit active accounts.
Even something as simple as a printed invoice or confirmation slip can reveal patterns. Regular deliveries signal consistent spending habits and predictable schedules, which can help thieves time their actions. Subscription boxes often include branding that identifies the service, which adds another layer of information. That visibility turns routine deliveries into potential clues for anyone paying attention.
Managing this risk involves a mix of awareness and small adjustments. Removing or shredding any paperwork tied to subscriptions keeps account details out of reach. Using digital receipts instead of printed ones reduces the amount of physical information floating around. Keeping track of active subscriptions also helps identify anything unusual quickly. Subscription services should add convenience, not create hidden vulnerabilities.
Don’t Let the Trash Tell Your Story
Trash should disappear quietly, not broadcast personal details to anyone willing to look. Every discarded item carries a piece of information, and those pieces can add up faster than expected. Taking control of what goes into the trash transforms it from a risk into a non-issue. Small habits like shredding, wiping devices, and removing labels create a strong barrier against unwanted attention.
What’s the most surprising item that could expose personal information, and what strategies make the biggest difference in keeping it safe? Share all of your thoughts, ideas, or even unexpected discoveries in the comments.
You May Also Like…
Received an Email About a Surprise Inheritance? 8 Reasons to Delete It Immediately
The Refund Scam Hitting During Filing Season and How to Avoid It
Scammers Are Cloning Official Report Sites and Here’s Where to File Safely
10 Everyday Behaviors That Can Increase Your Risk of Identity Theft
Data Breaches Keep Fueling Identity Theft and These Three Locks Add Protection
The post 6 Unexpected Ways Your Trash Can Be Used to Steal Your Information appeared first on Clever Dude Personal Finance & Money.








